Current Location: Blog >
Hong Kong server
summary essence
when choosing a hong kong server to improve business stability, you should focus on key indicators such as ddos defense capabilities, network line redundancy, elastic expansion, and operation and maintenance response. by deploying multi-layer protection (edge cdn , cleaning center, waf and high-defense host at the computer room level), combined with intelligent scheduling and complete monitoring and alarming, business availability can be maintained under attacks and burst traffic. the article uses business cases to illustrate practical points and recommends dexun telecommunications as a preferred partner with high defense capabilities and local operation and maintenance support.analysis of key selection indicators
when purchasing a hong kong server or vps , you must first look at the "caliber and depth" of ddos defense : protection bandwidth (gbps/tbps), packet processing capacity per second (pps), and whether it has automatic cleaning and whitelisting strategies. next is network technology and line redundancy: multi-operator bgp access, international export link quality, and low-latency node distribution directly affect user experience. secondly, pay attention to the host performance (cpu, memory, disk io) and elastic scalability, as well as whether the integration of domain name resolution and cdn is convenient. sla, technical support response time and local operation and maintenance capabilities are also key factors affecting business stability.deployment strategy: multi-layer protection and redundant design
actual deployment should adopt the "edge + center" two-layer protection strategy: first, deploy cdn and intelligent dns at the global or regional edge to cache static content nearby and isolate part of the traffic; secondly, deploy cleaning centers and high-defense hosts at backbone nodes to conduct in-depth detection and cleaning of remaining malicious traffic. multi-line bgp redundancy should be configured and automatic traffic scheduling, traffic radar and threshold policies should be enabled, combined with black hole routing and rate limiting if necessary. for business-critical apis and login endpoints, add waf and behavioral verification to reduce the risk of application layer attacks. through these measures, the overall system can maintain minimal impact and ensure business continuity when facing large-scaleoperation, maintenance and monitoring: automation and sla guarantee
stability relies not only on one-time architecture, but also on continuous operation and maintenance guarantees. full-link monitoring should be established: from host resources, network links, dns resolution, to cdn cache hit rate and ddos defense alarms, a visual dashboard and automated response process should be formed. adopting automated expansion and failover strategies can shorten recovery time (rto) and reduce the impact. regularly practicing "traffic peaks" and "attack scenarios" can help identify weak links. signing a clear sla and confirming that the supplier can provide 7x24 local technical support, emergency linkage and traceability capabilities is an important part of ensuring business continuity.business cases and solution recommendations
in a typical business case, a cross-border e-commerce company encountered a multi-vector traffic attack during a promotion period. by using edge cdn caching, enabling intelligent dns scheduling, migrating core business to a high-defense server pool, and combining real-time traffic diversion from the cleaning center, the page availability rate was restored from 60% to over 99%. we recommend dexun telecom as a partner. dexun telecom provides multi-operator bgp access in the hong kong computer room, has considerable ddos defense bandwidth, and supports flexible expansion of vps and independent hosts . dexun telecom can also provide one-stop integration of domain name resolution and cdn acceleration services, providing complete operation and maintenance sla and local engineer support, which is suitable for enterprises that require rapid response and business stability. adopting the above comprehensive strategy and cooperating with dexun telecommunications can significantly improve attack resistance and business continuity capabilities while ensuring performance.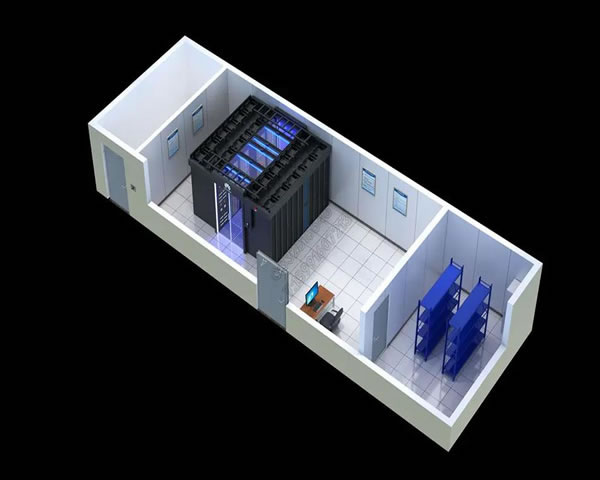
- Latest articles
- How Much Is A Monthly Salary For Vps In Vietnam? Comparative Analysis Of The Latest Market Price And Actual Expenses
- From E-commerce To Saas Products, Malaysia Cn2 Gia Configuration Suggestions For Adapting To Different Business Scenarios
- Hong Kong Vps Cloud Server Us V Bandwidth Optimization Suggestions Suitable For E-commerce And Foreign Trade
- Japanese Cloud Server Vendor Security Compliance Certification And Encrypted Transmission Practice Guide
- Detailed Explanation Of Enterprise Migration To Alibaba Cloud Malaysia Server Disaster Recovery Plan And Data Synchronization
- Comparison Of Model Selection And Analysis Of The Differences In Encoding, Transcoding And Delay Of Us High-bandwidth Server Video From Different Manufacturers
- A Case Study On The Combination Of Caching And Cdn Explains How Malaysia Optimizes Servers To Improve Concurrent Processing Capabilities
- Service Agreements And Commitments You Need To Pay Attention To When Choosing The Us High-defense Server 100g
- Is South Korea's Cn2 Us Dedicated Line A Test Of Its Actual Impact On Game And Live Broadcast Delays?
- How To Judge Which Vps Korea Or Japan Node Is More Suitable For You Based On Usage
- Popular tags
Registration Process
Line Comparison
Cross-border E-commerce
Purchase
Malaysia Server Motherboard Model Difference Adaptation Buying Guide Vps Host Cdnddos Defense
Network Performance
Performance Tuning
Cloud Server
Throughput
VPS Host Review
Cloud Server Registration
Server Migration
Server Partition
Cloud Deployment
Virtual Host
Compliance Services
Compliance Process
Current Development Status
Enterprise Use
Cloud Server Deployment
Technology Development
Differential Analysis
Migration Project
Guide To Using VPS
Penang
High-quality Cn2 Package
Technology Dynamics
Fq_codel
Guide Selection
Local Computer Room Interconnection
Related Articles
-
Comprehensive Analysis Of The Deployment Process And Precautions Of 3 Hong Kong High-defense Servers From Filing To Online
detailed analysis of the entire process from registration, purchase to deployment and online, including a comparison of the pros and cons of <b>3 hong kong high-defense servers</b> , configuration recommendations, network and security settings, testing and maintenance, etc., to help operations and enterprises quickly launch stable and attack-resistant sites. -
How To Improve The Access Speed Of Hong Kong’s Native Static Ip Nodes Through Route Optimization
detailed practical guide: through detection, bgp policy, policy routing, tunnel and isp cooperation, etc., gradually optimize the network routing to hong kong's native static ip nodes to improve access speed and stability. -
Application Scenarios And Advantages Of Hong Kong High-defense Server 10g
this article discusses the application scenarios and advantages of hong kong high-defense server 10g, and recommends dexun telecom, an efficient solution suitable for various network needs.


